Your browser doesn't support the features required by impress.js, so you are presented with a simplified version of this presentation.
Securing Your Django Site
DjangoSD - February 22, 2012
Web security basics: XSS
def testview(request): t = Template("Hello my name is {{ name }}") c = Context({'name': "<script>alert('owned')</script>"}) return HttpResponse(t.render(c))
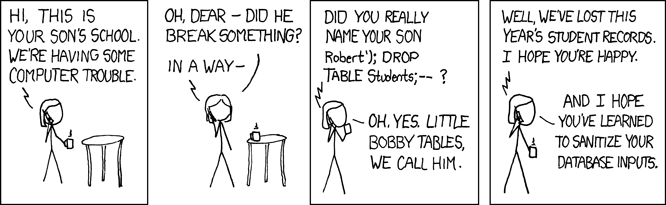
Web security basics: SQL Injection
Post.objects.get(name="'; DELETE FROM blog_post; --")
Web security basics: CSRF
Explaining CSRF in a one-liner is tough.
Bear with me...
<img src="http://chase.com/xfer?from=you&to=me&amount=1000" />
This security thing is easy...

Double check your exceptions!
.raw()
.extra()
mark_safe()
@csrf_exempt
The Not-So-Basics: Caching
Is this safe?
@cache_page(60 * 15) def my_view(request): ...
Caching: It depends
- Is your cache backend secure?
- Shared host?
- Are you using pickle?
The pickle module is not intended to be secure against erroneous or maliciously constructed data. Never unpickle data received from an untrusted or unauthenticated source.
The Not-So-Basics: Passwords
Passwords (continued)
- Password sniffing? (HTTPS)
- No hashed passwords in public source control!
- Improvements coming in Django 1.4
The Not-So-Basics: Misc

- Clickjacking
- SECRET_KEY
- Uploaded files
- Denial of service
- Shell injection
New Django Features: Signing
from django.core.signing import TimestampSigner signer = TimestampSigner() value = signer.sign('time sensitive')

Did I mention to keep your SECRET_KEY a secret?
Securing Your Server
- HTTPS: SESSION_COOKIE_SECURE
- Uploaded files: LimitRequestBody
- Throttling: HttpLimitReqModule, Apache modules
- Firewalls: IPTables
Tools to Secure Your Site
- Django apps: django-secure
- Web app firewalls: mod-security
- Port scanner: nmap
Thanks!
https://docs.djangoproject.com/en/dev/topics/security/